While the initial shock of a tremendously personal data breach of Equifax has subsided, two Goizueta Business School professors have said the fallout could go on for years, or even a decade.
In late September, embattled Equifax CEO Richard Smith stepped down, less than a month after the credit reporting agency announced that a hack to its computer system exposed the sensitive personal information of 143 million Americans. In recent weeks, it was reported that nearly 11 million driver’s licenses were among the data in the breach.
The fallout has been significant, from top leadership stepping down, to the stock price dropping some 40 percent before a small rebound.
Overall, three top executives stepped down, and interim CEO Paulino do Rego Barros, Jr., most recently president of the Asia Pacific region, replaced Smith. Equifax is also facing several state and federal inquiries, class-action lawsuits and congressional investigations.
Earlier this month, the IRS temporarily suspended the $7.2 million, no-bid contract it awarded to Equifax to verify the identities of taxpayers when they create accounts on its website.
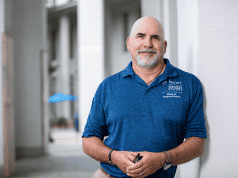
Peter Topping, associate professor in the Practice of Organization & Management at Goizueta, said previous hacks of companies like Target, Home Depot and Yahoo may suggest the recovery period would be relatively short, the scope of this breach, and the fact that the company is supposedly in the business of secure information, may extend this to a two-year time frame.
“The story for the consumers affected by the breach is likely to go on for many years,” Topping said. “It is my understanding that the potential for fraudulent usage of the stolen data can still be possible 10+ years later. The story for Equifax is more likely to be resolved over the next 12 to 18 months. The search for, and onboarding of, a new CEO can take that amount of time.”
Kevin Crowley, a lecturer of Finance at Goizueta, noted that the stock price dropped from an early September high of about $142 per share, to about $94 in mid-September. It has recovered to trading at about $109.
“That’s a normal reaction to what was a huge negative news story for the company and right now, it’s sort of stabilized,” Crowley said. “Initially, value investors may have jumped at it seeing it was trading down close to 40 percent. But the hard thing here is how it plays out over the next 12 to 18 months. If we observe a meaningful increase in the incidence of credit card fraud or the like, I think that will weigh on the stock price. The stock is unlikely to get back to prior highs very soon, because it’s not a situation where they can say the coast is clear now.”
As Equifax looks to rebuild public trust, it must first look internally, Topping said, especially in how it selects new senior leadership and how they react to fixing the problem.
“The first step is to establish or regain trust within the organization itself,” Topping said. “The public evidence that has surfaced from the former CEO indicates that he was unwilling to accept responsibility, but had no difficulty blaming others. If this pervades in the top echelon of the company, then the corporate culture will work against rebuilding trust with the public and investors. If all of the employees at Equifax believe in the company and its commitment to data security, that will be communicated outward in myriad ways. It’s not just a matter of time, it’s more a matter of effective senior leadership.”
Another credit monitoring firm, TransUnion, reacted to the Equifax news by bolstering its lobbying effort in Washington. Reuters reported that TransUnion, which already had three lobbying shops under contract, added CGCN Group, a Republican firm that lobbies on a myriad of topics, according to disclosures filed with the U.S. Congress.
Crowley said he believes the other agencies in the credit monitoring space are also working harder than they have in the past to bolster their security. And given the attention the incident has received, it could signal a shift in how personal information is stored and shared.
“We’re losing the arms race against the hackers. Something has to change,” Crowley said. “Using Social Security numbers and passwords and simple things like that, they’re just not as effective as they were in the past. I’m sure this will give rise to new products and new types of security. More money needs to be spent on R&D for security.”
Topping added that the issue should be a lesson to companies in general about management.
“From a leadership perspective, the lesson to learn is the importance of being more ‘hands-on’ with their upper mid-level managers,” he said. “To have one person identified as being responsible for the breach indicates an organization that was too disengaged with the security system.”